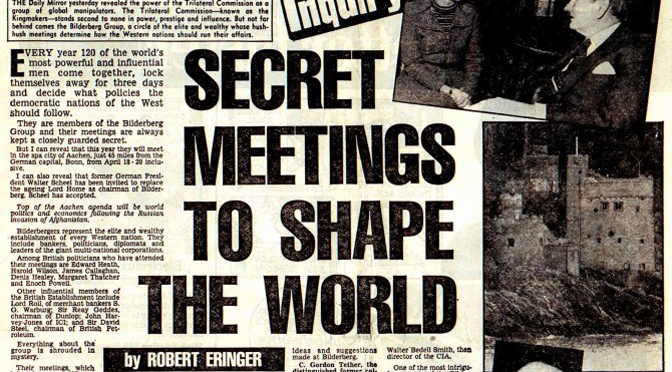
Interesting article about how Illuminati organized Hitler to power and used him as a tool:
The pre-war British establishment was Illuminati and Communist to the core.
They put Hitler into power in Germany and then maneuvered him into a war that would destroy Germany as an independent country once and for all.
(from Sept. 2006)
by Henry Makow Ph.D.
In Dec. 1942 Heinrich Mueller, Chief of the Gestapo, rolled up the Soviet spy network in mainland Europe and secured a list of Soviet agents and informants in England that reads like a “who’s who” of the British establishment and lifts the veil from modern history.

(Gestapo Chief Heinrich Muller)
Soviet spies include Edward Wood, Lord Halifax, Neville Chamberlain’s Foreign Secretary and an architect of the “Appeasement” policy.
Appeasement encouraged Hitler to think England wanted him to expand eastward against the Soviet Union. In fact, Halifax was Illuminati like the Communists. Appeasement was designed to trap Hitler in a two-front war which would level Germany (and Europe) and kill sixty million people.
Mueller’s list of spies includes Victor Rothschild, the head of the central banking dynasty, one of the “Cambridge Five” traitors. Curiously, the other four (Burgess, Maclean, Blunt and Philby) aren’t on Mueller’s list. Halifax’s son married a Rothschild.
The list also includes Charles Hambro, another banker of Jewish origin who was part of a Bank of England decision to continue financing Nazism in 1934 as a “stabilizing influence.” Obviously, as a Soviet asset, this man was not pro-Nazi. The explanation is that both Nazism and Communism are Illuminati creations.
The list also includes Sir Robert Waley-Cohen and many members of the anti-appeasement “Focus” group that funded Winston Churchill. Waley-Cohen was the Chairman of the Rothschild-controlled Shell Oil and the leader of the British Jewish Community.
Other bankers, banking scions and industrialists include Eugen Spier, Maurice Baring, Leonard Montefiore, Edward Guggenheim, Sir Robert Mond and Sir Phillip Sassoon. All are of Jewish origin.
Prominent Labor Party and trade union leaders included Ernest Bevin, Harold Laski, Herbert Stanley Morrison and Sir Walter Citrine. Members of ancient aristocratic families include Richard Combe Abdy, Baron Strabogli, and Admiral Reginald Plunkett-Ernle-Erle-Drax. There was press mogul J.S. Elias, cartoonist Victor Weisz and Daily Express Chairman Ralph D. Blumenfeld.
Prominent civil servants include Rex Leeper of the Foreign Office ruling clique and Sir Maurice Hankey, who as cabinet secretary and Clerk of the Privy Council (1919-1938) knew all the secrets. There was Slavonic scholar Bernard Pares and Jurist Sir Hirsch Lauterpacht. (The complete agent list is at the end of this article.)
FREEMASONS
What did this disparate group have in common? About half of them are recognizably Jewish. But the connection that binds all of them likely is the Illuminati, the top rung of Freemasonry. Its aim is to weaken mankind through a series of contrived wars in order to establish a Masonic or “Illuminist” world dictatorship dedicated to the “light giver” Lucifer (their alter ego.) Obama, Bush, Clinton, Kerry etc. are all members.
The Illuminati started Communism. Their common anniversary is May 1; their common symbol is the satanic inverted pentagram. They funded the Bolshevik Revolution and secretly ran the USSR, which was a model for the New World Order. Far from being spies for Stalin, some of these men probably were his superiors.
Soviet Russia was a dummy-state creation of the London-based Illuminati bankers. The Second World War, the Cold War, and now the “War on Terror” are all their inventions. They are responsible for 9-11 and for the neopagan assault on Western Civilization, Christianity and Islam (incl. family, nation, race, morality and truth) that we call modernism, humanism and globalism.
Heinrich Mueller died in California in 1983. The CIA recruited Mueller in Switzerland in 1948 and paid him $1 million for an Interrogation running 1000-pages that includes this list. Mueller left his microfilmed archives to his nephew, “Douglas Gregory” who has published a part.
BAIT AND SWITCH
The Bank of England funded the rise of Adolf Hitler through the Schroder Bank.
(Tiarcks and his granddaughter)
F.C. Tiarcks, the Managing Director of the Schroder Bank, was also a Director of the Bank of England.
Eustace Mullins writes: “Because his own financial backers, the Schroders, were sponsoring the Appeasement Party, Hitler believed there would be no war [with England.] He did not suspect that the backers of the Appeasement Party, now that Chamberlain had served his purpose in duping Hitler, would cast Chamberlain aside and make Churchill the Prime Minister.” (The Secrets of the Federal Reserve, pp.76-78.)
While history portrays Hitler as duping the naive Neville Chamberlain and Lord Halifax, it appears Hitler himself was tricked into thinking he could expand eastward with impunity. Neville Chamberlain wasn’t in on the secret. (He died prematurely just months after leaving office.) But as a Soviet informant, Halifax certainly was instrumental.
As an early opponent of British rearmament, Halifax encouraged Hitler’s plans and later complimented the dictator for being a “genuine hater of Communism.” In 1937, Halifax actually offered Hitler changes in the “European Order” in regard to Danzig, Austria and Czechoslovakia.
“It was Halifax not Hitler who first mentioned by name the areas where the Versailles Treaty might be reinterpreted to Germany’s benefit,” writes historian Andrew Roberts. “Halifax did the one thing which Eden had told him not to, and which Vansittart warned would ‘bring the European card-castle tumbling down.’ Moreover he did it not once but thrice in the course of the conversations.” (The Holy Fox: A Biography of Lord Halifax, 1991, pp. 67, 70-71.)
Halifx’s closest adviser was Philip Kerr, Lord Lothian, a member of the Rothschild-Milner-Rhodes Round Table secret society (i.e the Illuminati). According to Roberts, Lothian was “a friend of Halifax’s and had non-parliamentary political influence of a type seldom seen in today’s politics.” (109)
Appeasement was designed to encourage Hitler to take action which would justify a declaration of war by the West.
“What we want to secure is the certainty of a war on two-fronts,” Halifax said in March 1939. (Roberts, 146) Halifax was responsible for the foolhardy British guarantee of Poland that led to this war declaration in Sept. 1939. The USSR also invaded Poland but there was no declaration of war against it. Stalin was pre-primed to attack the Nazis in 1941.(This is essentially the deal Christian Rakovsky offered Stalin 1938.)
The whole knuckle-biting drama of war and peace in 1939-41, including England as the lonely defender of freedom, was a charade. Germany was in the cross-hairs all along. Could the USA be in the same position today as Russia and China prepare for war?
The appeasers and their opponents were two Illuminati house teams pursuing common goals. Lady Astor’s Cliveden Manor was supposed to be the HQ of the (pro-Nazi) appeasement party but, as Andrew Roberts points out, arch anti-appeasers like Duff Cooper, Anthony Eden and Russian Foreign Minister Maxim Litvinov (nee Meir Finkelstein) were regular guests. (67)
CONCLUSION
Wars are the artificial creation of the Illuminati, a satanic cult that extends its tentacles over the whole planet. “Muller’s List” provides a glimpse at the composition of this group: bankers, industrialists, aristocrats, military, scholars, trade unionists and media.
There are a lot of Jews but it should be obvious that the Illuminati victimized Jews as much as anyone. Jews have been the canon fodder for Communism, Zionism and Nazism. Instead of defending the Illuminati, Jews should revile it. Otherwise they appear to be in collusion.
Possibly some listees didn’t realize what they were advancing. The Illuminati pretended to oppose fascism. Today they pretend to build a humanist utopia, an answer to poverty, disease, and prejudice. Former World Bank President James Wolfensohn had the slogan “Plutocrat for the Poor” on his web site.
Hitler was groomed and funded for the purpose of destroying Germany’s national aspirations and to provide a pretext for the State of Israel. The Illuminati starts wars to destroy nation states, demoralize humanity, consolidate power and produce huge profits and debt slavery. This cult, which has a stranglehold on thought and expression, pretty much defines realty. Our best course is to find our truth from different sources and define reality anew.
———
“Mueller’s List” from Douglas Gregory, “Gestapo Chief: The 1948 Interrogation of Heinrich Muller Vol. 3 p.107.
Lt. Col. Frederick William Abbot
Sir Maurice Hankey
Richard Combe Abdy
Eugen Spier
George Dixon Abraham
Baron Strabogli
Frederick Edward Fox Adam
J.S. Elias, Baron Southwood
Admiral Sir Percy Addison
Sir H.L. Rothband
Elkan Nathan Adler
Sir E.L. Goschen
Admiral Oliver Backhouse
Mrs. Blanche Dugdale
John Ball
Sir Robert Wood
Maurice Baring
Sir Robert Mond
Ralph D. Blumenfeld
Jurgen Kuczynski
Sir Harry Robert Boyd
Sir Robert Waley-Cohen
Sir Charles Hambro
Rex Leeper
Edward Wood (Lord Halifax)
Sir Walter Citrine
Walter Rosenhain
Victor Rothschild
Charles Masterman Herz
Sir Philip Sassoon
Victor Weisz
Sir Bernard Pares
Friedrich Saxl
Ernest Bevin
Sir Hirsch Lauterpacht
Herbert Stanley Morrison
Harold Joseph Laski
Sir Reginald Plunkett-Erle-Drax
Edward Armand Guggenheim
Source
Read more from Auricmedia:
[carousel-horizontal-posts-content-slider]
, took over the leadership.
was one of the order’s most famous members before he left to really get his freak on.





 33rd Degree Masonic Philosopher, Manly P. Hall describes this event in his Gnostic masterpiece, “The
33rd Degree Masonic Philosopher, Manly P. Hall describes this event in his Gnostic masterpiece, “The