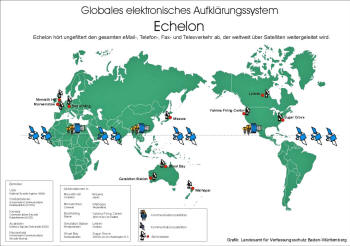
Sometimes there are floating interesting documents about how military possesses alien technology and here is something interesting:
Drones:
Military Reverses Alien Technology
© 2007 by “Isaac.”
Aliens use symbols to control their technology
Note: This technology was reverse engineered over 30 years ago. Of course, you are not permitted to know about or utilize this technology. In fact, should you somehow invent or discover this technology and should it become known, your technology will be confiscated for “national security” purposes and you will be told to maintain silence. Should you disobey, you will be dealt with.
Here is the brief introduction. I’m using the alias Isaac, and used to work in what was called the CARET program in the 80’s. During my time there, I worked with a lot of the technology that is clearly at work in the recent drone/strange craft sightings, most notably the “language” and diagrams seen on the underside of each craft. What follows is a lengthy letter about who I am, what I know, and what these sightings are (probably) all about.
The appearance of these photos has convinced me to release at least some of the numerous photographs and photocopied documents I still possess some 20 years later that can explain a great deal about these sightings. On this site you will find some of these. They are available as high resolution scans that I am giving away free, PROVIDED THEY ARE NOT MODIFIED IN ANY WAY AND ARE KEPT TOGETHER ALONG WITH THIS WRITTEN MATERIAL.
I am also trying to get in touch with the witnesses so far, such as Chad, Rajman, Jenna, Ty, and the Lake Tahoe witness (especially Chad). I have advice for them that may be somewhat helpful in dealing with what they’ve seen and what I would recommend they do with what they know. If you are one of these witnesses, or can put me in touch with them, please contact Coast to Coast AM and let them know.
My Experience with the CARET Program and Extra-terrestrial Technology
Isaac, June 2007
This letter is part of a package I’ve assembled for Coast to Coast AM to distribute to its audience. It is a companion to numerous document and photo scans and should not be separated from them.
You can call me Isaac, an alias I’ve chosen as a simple measure of protection while I release what would be called tremendously sensitive information even by today’s standards. “Sensitive” is not necessarily synonymous with “dangerous”, though, which is why my conscience is clear as I offer this material up for the public. My government has its reasons for its continual secrecy, and I sympathize with many of them, but the truth is that I’m getting old and I’m not interested in meeting my maker one day with any more baggage than necessary! Furthermore, I put a little more faith in humanity than my former bosses do, and I think that a release of at least some of this info could help a lot more than it could hurt, especially in today’s world.
I should be clear before I begin, as a final note: I am not interested in making myself vulnerable to the consequences of betraying the trust of my superiors and will not divulge any personal information that could determine my identity. However my intent is not to deceive, so information that I think is too risky to share will be simply left out rather than obfuscated in some way (aside from my alias, which I freely admit is not my real name). I would estimate that with the information contained in this letter, I could be narrowed down to one of maybe 30-50 people at best, so I feel reasonably secure.
Some Explanation for the Recent Sightings
For many years I’ve occasionally considered the release of at least some of the material I possess, but the recent wave of photos and sightings has prompted me to cut to the chase and do so now.
I should first be clear that I’m not directly familiar with any of the crafts seen in the photos in their entirety. I’ve never seen them in a hangar or worked on them myself or seen aliens zipping around in them. However, I have worked with and seen many of the parts visible in these crafts, some of which can be seen in the Q3-85 Inventory Review scan found at the top of this page. More importantly though, I’m very familiar with the “language” on their undersides seen clearly in photos by Chad and Rajman, and in another form in the Big Basin photos.
One question I can answer for sure is why they’re suddenly here. These crafts have probably existed in their current form for decades, and I can say for sure that the technology behind them has existed for decades before that. The “language”, in fact, (I’ll explain shortly why I keep putting that in quotes) was the subject of my work in years past. I’ll cover that as well.
The reason they’re suddenly visible, however, is another matter entirely. These crafts, assuming they’re anything like the hardware I worked with in the 80’s (assuming they’re better, in fact), are equipped with technology that enables invisibility. That ability can be controlled both on board the craft, and remotely. However, what’s important in this case is that this invisibility can also be disrupted by other technology. Think of it like radar jamming.
I would bet my life savings (since I know this has happened before) that these craft are becoming visible and then returning to invisibility arbitrarily, probably unintentionally, and undoubtedly for only short periods, due to the activity of a kind of disrupting technology being set off elsewhere, but nearby. I’m especially sure of this in the case of the Big Basin sightings, were the witnesses themselves reported seeing the craft just appear and disappear. This is especially likely because of the way the witness described one of the appearances being only a momentary flicker, which is consistent with the unintentional, intermittent triggering of such a device.
It’s no surprise that these sightings are all taking place in California, and especially the Saratoga/South Bay area. Not far from Saratoga is Mountain View/Sunnyvale, home to Moffett Field and the NASA Ames Research center. Again, I’d be willing to bet just about anything that the device capable of hijacking the cloaking of these nearby craft was inadvertently triggered, probably during some kind of experiment, at the exact moment they were being seen.
Miles away, in Big Basin, the witnesses were in the right place at the right time and saw the results of this disruption with their own eyes. God knows what else was suddenly appearing in the skies at that moment, and who else may have seen it. I’ve had some direct contact with this device, or at least a device capable of the same thing, and this kind of mistake is not unprecedented. I am personally aware of at least one other incident in which this kind of technology was accidentally set off, resulting in the sudden visibility of normally invisible things. The only difference is that these days, cameras are a lot more common!
The technology itself isn’t ours, or at least it wasn’t in the 80’s. Much like the technology in these crafts themselves, the device capable of remotely hijacking a vehicle’s clacking comes from a non-human source too. Why we were given this technology has never been clear to me, but it’s responsible for a lot. Our having access to this kind of device, along with our occasionally haphazard experimentation on them, has lead to everything from cloaking malfunctions like this to full-blown crashes. I can assure you that most (and in my opinion all) incidents of UFO crashes or that kind of thing had more to do with our meddling with extremely powerful technology at an inopportune time than it did mechanical failure on their part. Trust me, those things don’t fail unless something even more powerful than them makes them fail (intentionally or not).
Think of it like a stray bullet. You can be hit by one at any time, without warning, and even the shooter didn’t intent to hit you. I can assure you heads are rolling over this as well. If anyone notices a brilliant but sloppy physicist patrolling the streets of Baghdad in the next couple weeks, I’d be willing to guess how he got there. (I kid, of course, as I certainly hope that hasn’t actually happened in this case)
I’d now like to explain how it is that I know this.
The CARET Program
My story begins the same as it did for many of my co workers, with graduate and post-graduate work at university in electrical engineering. And I had always been interested in computer science, which was a very new field at the time, and my interest piqued with my first exposure to a Tixo during grad school. In the years following school I took a scenic route through the tech industry and worked for the kinds of companies you would expect, until I was offered a job at the Department of Defense and things took a very different turn.
My time at the DoD was mostly uneventful but I was there for quite a while. I apparently proved myself to be reasonably intelligent and loyal. By 1984 these qualities along with my technical background made me a likely candidate for a new program they were recruiting for called “CARET”.
Before I explain what CARET was I should back up a little. By 1984, Silicon Valley had been a juggernaut of technology for decades. In the less than 40 years since the appearance of Shockley’s transistor this part of the world had already produced a multi billion dollar computer industry and made technological strides that were unprecedented in other fields, from hypertext and online collaboration in ’68 to the Alto in ’73.
Private industry in Silicon Valley was responsible for some of the most incredible technological leaps in history and this fact did not go unnoticed by the US government and military. I don’t claim to have any special knowledge about Roswell or any of the other alleged early UFO events, but I do know that whatever the exact origin, the military was hard at work trying to understand and use the extra-terrestrial artifacts it had in its possession. While there had been a great deal of progress overall, things were not moving as quickly as some would have liked. So, in 1984, the CARET program was created with the aim of harnessing the abilities of private industry in silicon valley and applying it to the ongoing task of understanding extra-terrestrial technology.
One of the best examples of the power of the tech sector was Xerox PARC, a research center in Palo Alto, CA. XPARC was responsible for some of the major milestones in the history of computing. While I never had the privilege of working there myself I did know many of the people who did and I can say that they were among the brightest engineers I ever knew.
XPARC served as one of the models for the CARET program’s first incarnation, a facility called the Palo Alto CARET Laboratory (PACL, lovingly pronounced “packle” during my time there). This was where I worked, along with numerous other civilians, under the auspices of military brass who were eager to find out how the tech sector made so much progress so quickly. My time at the DoD was a major factor behind why I was chosen, and in fact about 30+ others who were hired around the same time had also been at the Department about as long, but this was not the case for everyone. A couple of my co-workers were plucked right from places like IBM and, at least two of them came from XPARC itself. My DoD experience did make me more eligible for positions of management, however, which is how I have so much of this material in my possession to begin with.
So in other words, civilians like myself who had at–at most–some decent experience working for the DoD but no actual military training or involvement, were suddenly finding ourselves in the same room as highly classified extra-terrestrial technology. Of course they spent about 2 months briefing us all before we saw or did anything, and did their best to convince us that if we ever leaked a single detail about what we were being told, they’d do everything short of digging up our ancestors and putting a few slugs in them too just for good measure. It seemed like there was an armed guard in every corner of every room. I’d worked under some pretty hefty NDAs in my time but this was so far out of my depth I didn’t think I was going to last 2 weeks in an environment like that.
But amazingly things got off to a good start. They wanted us, plain and simple, and our industry had shown itself to be so good at what it did that they were just about ready to give us carte blanche.
Of course, nothing with the military is ever that simple, and as is often the case they wanted to have their cake and eat it too. What I mean by this is that despite their interest in picking our brains and learning whatever they could from our way of doing things, they still wanted to do it their way often enough to frustrate us.
At this point I’m going to gloss over the emotional side of this experience, because this letter isn’t intended to be a memoir, but I will say that there’s almost no way to describe the impact this kind of revelation has on your mind. There are very few moments in life in which your entire world view is turned forever upside down, but this was one of them.
I still remember that turning point during the briefing when I realized what he’d just told us, and that I hadn’t heard him wrong, and that it wasn’t some kind of joke. In retrospect the whole thing feels like it was in slow motion, from that slight pause he took just before the term “extra-terrestrial” came out for the first time, to the way the room itself seemed to go off kilter as we collectively tried to grasp what was being said. My reflex kept jumping back and forth between trying to look at the speaker, to understand him better, and looking at everyone else around me, to make sure I wasn’t the only one that was hearing this.
At the risk of sounding melodramatic, it’s a lot like a child learning his parents are divorcing. I never experienced that myself, but a very close friend of mine did when were boys, and he confided in me a great deal about what the experience felt like. A lot of what he said would aptly describe what I was feeling in that room. Here was a trusted authority figure telling you something that you just don’t feel ready for, and putting a burden on your mind that you don’t necessarily want to carry. The moment that first word comes out, all you can think about it is what it was like only seconds ago, and knowing that life is never going to be as simple as it was then. After all that time at the DoD, I thought I at least had some idea of what was going on in the world, but I’d never heard so much as a peep about this. Maybe one day I’ll write more on this aspect, because it’s the kind of thing I really would like to get off my chest, but for now I’ll digress.
Unlike traditional research in this area, we weren’t working on new toys for the air force. For numerous reasons, the CARET people decided to aim its efforts at commercial applications rather than military ones. They basically wanted us to turn these artifacts into something they could patent and sell. One of CARET’s most appealing promises was the revenue generated by these product-ready technologies, which could be funneled right back into black projects. Working with a commercial application in mind was also yet another way to keep us in a familiar mind state. Developing technology for the military is very different than doing so for the commercial sector, and not having to worry about the difference was another way that CARET was very much like private industry.
CARET shined in the way it let us work the way we were used to working. They wanted to recreate as much of the environment we were used to as they could without compromising issues like security. That meant we got free reign to set up our own workflow, internal management structure, style manuals, documentation, and the like. They wanted this to look and feel like private industry, not the military. They knew that was how to get the best work out of us, and they were right.
But things didn’t go as smoothly when it came to matters like access to classified information. They were exposing what is probably their single biggest secret to a group of people who had never even been through basic training and it was obvious that the gravity of this decision was never far from their minds. We started the program with a small set of extra-terrestrial artifacts along with fairly elaborate briefings on each as well as access to a modest amount of what research had already been completed.
It wasn’t long before we realized we needed more though, and getting them to provide even the smallest amount of new material was like pulling teeth. CARET stood for “Commercial Applications Research for Extra-terrestrial Technology”, but we often joked that it should have stood for “Civilians Are Rarely Ever Trusted.”
PACL was located in Palo Alto, but unlike XPARC, it wasn’t at the end of a long road in the middle of a big complex surrounded by rolling hills and trees. PACL was hidden in an office complex owned entirely by the military but made to look like an unassuming tech company.
From the street, all you could see was what appeared to be a normal parking lot with a gate and a guard booth, and a 1-story building inside with a fictitious name and logo. What wasn’t visible from the street was that behind the very first set of doors was enough armed guards to invade Poland, and 5 additional underground stories. They wanted to be as close as possible to the kinds of people they were looking to hire and be able to bring them in with a minimum of fuss.
Inside, we had everything we needed. State of the art hardware and a staff of over 200 computer scientists, electrical engineers, mechanical engineers, physicists and mathematicians. Most of us were civilians, as I’ve said, but some were military, and a few of them had been working on this technology already. Of course, you were never far from the barrel of a machine gun, even inside the labs themselves (something many of us never got used to), and bi-weekly tours were made by military brass to ensure that not a single detail was out of line. Most of us underwent extensive searches on our way into and out of the building. There it was, probably the biggest secret in the world, in a bunch of parts spread out on laboratory tables in the middle of Palo Alto so you can imagine their concern.
One downside to CARET was that it wasn’t as well-connected as other operations undoubtedly were. I never got to see any actual extra-terrestrials (not even photos), and in fact never even saw one of their complete vehicles. 99% of what I saw was related to the work at hand, all of which was conducted within a very narrow context on individual artifacts only. The remaining 1% came from people I met through the program, many of which working more closely with “the good stuff” or had in the past.
In fact, what was especially amusing about the whole affair was the way that our military management almost tried to act as if the technology we were essentially reverse engineering wasn’t extra-terrestrial at all. Aside from the word “extra-terrestrial” itself, we rarely heard any other terms like “alien” or “UFO” or “outer space” or anything. Those aspects were only mentioned briefly when absolutely necessary to explain something. In many cases it was necessary to differentiate between the different races and their respective technology, and they didn’t even use the word “races”. They were referred to simply as different “sources”.
The Technology
A lot of the technology we worked on was what you would expect, namely antigravity. Most of the researchers on the staff with backgrounds in propulsion and rocketry were military men, but the technology we were dealing with was so out of this world that it didn’t really matter all that much what your background was because none of it applied.
All we could hope to do was use the vocabulary of our respective fields as a way to model the extremely bizarre new concepts we were very slowly beginning to understand as best we could. A rocket engineer doesn’t usually rub elbows much with a computer scientist, but inside PACL, we were all equally mystified and were ready to entertain any and all ideas.
The physicists made the most headway initially because out of all of our skills, theirs overlapped the most with the concepts behind this technology (although that isn’t saying much!) Once they got the ball rolling though, we began to find that many of the concepts found in computer science were applicable as well, albeit in very vague ways. While I didn’t do a lot of work with the antigrav hardware myself, I was occasionally involved in the assessment of how that technology was meant to interface with its user.
The antigrav was amazing, of course, as were the advances we were making with materials engineering and so on. But what interested me most then, and still amazes me most to this day, was something completely unrelated. In fact, it was this technology that immediately jumped out at me when I saw the Chad and Rajman photos, and even more so in the Big Basin photos.
The “Language”
I put the word Language in quotes because calling what I am about to describe a “language” is a misnomer, although it is an easy mistake to make.
Their hardware wasn’t operated in quite the same way as ours. In our technology, even today, we have a combination of hardware and software running almost everything on the planet. Software is more abstract than hardware, but ultimately it needs hardware to run it. In other words, there’s no way to write a computer program on a piece of paper, set that piece of paper on a table or something, and expect it to actually do something. The most powerful code in the world still doesn’t actually do anything until a piece of hardware interprets it and translates its commands into actions.
But their technology is different. It really did operate like the magical piece of paper sitting on a table, in a manner of speaking. They had something akin to a language, that could quite literally execute itself, at least in the presence of a very specific type of field. The language, a term I am still using very loosely, is a system of symbols (which does admittedly very much resemble a written language) along with geometric forms and patterns that fit together to form diagrams that are themselves functional. Once they are drawn, so to speak, on a suitable surface made of a suitable material and in the presence of a certain type of field, they immediately begin performing the desired tasks. It really did seem like magic to us, even after we began to understand the principles behind it.
I worked with these symbols more than anything during my time at PACL, and recognized them the moment I saw them in the photos. They appear in a very simple form on Chad’s craft, but appear in the more complex diagram form on the underside of the Big Basin craft as well. Both are unmistakable, even at the small size of the Big Basin photos. An example of a diagram in the style of the Big Basin craft is included with this in a series of scanned pages from the [mistitled] “Linguistic Analysis Primer”. We needed a copy of that diagram to be utterly precise, and it took about a month for a team of six to copy that diagram into our drafting program!
Explaining everything I learned about this technology would fill up several volumes, but I will do my best to explain at least some of the concepts as long as I am taking the time to write all this down.
First of all, you wouldn’t open up their hardware to find a CPU here, and a data bus there, and some kind of memory over there. Their hardware appeared to be perfectly solid and consistent in terms of material from one side to the other. Like a rock or a hunk of metal.
But upon [much] closer inspection, we began to learn that it was actually one big holographic computational substrate – each “computational element” (essentially individual particles) can function independently, but are designed to function together in tremendously large clusters. I say its holographic because you can divide it up into the smallest chunks you want and still find a scaled-down but complete representation of the whole system. They produce a nonlinear computational output when grouped.
So 4 elements working together is actually more than 4 times more powerful than 1. Most of the internal “matter” in their crafts (usually everything but the outermost housing) is actually this substrate and can contribute to computation at any time and in any state. The shape of these “chunks” of substrate also had a profound effect on its functionality, and often served as a “shortcut” to achieve a goal that might otherwise be more complex.
So back to the language. The language is actually a “functional blueprint”. The forms of the shapes, symbols and arrangements thereof is itself functional. What makes it all especially difficult to grasp is that every element of each “diagram” is dependant on and related to every other element, which means no single detail can be created, removed or modified independently. Humans like written language because each element of the language can be understood on its own, and from this, complex expressions can be built. However, their “language” is entirely context-sensitive, which means that a given symbol could mean as little as a 1-bit flag in one context, or, quite literally, contain the entire human genome or a galaxy star map in another.
The ability for a single, small symbol to contain, not just represent, tremendous amounts of data is another counter-intuitive aspect of this concept.
We quickly realized that even working in groups of 10 or more on the simplest of diagrams, we found it virtually impossible to get anything done. As each new feature was added, the complexity of the diagram exponentially grew to unmanageable proportions. For this reason we began to develop computer-based systems to manage these details and achieved some success, although again we found that a threshold was quickly reached beyond which even the supercomputers of the day were unable to keep up. Word was that the extra-terrestrials could design these diagrams as quickly and easily as a human programmer could write a Fortran program. It’s humbling to think that even a network of supercomputers wasn’t able to duplicate what they could do in their own heads. Our entire system of language is based on the idea of assigning meaning to symbols. Their technology, however, somehow merges the symbol and the meaning, so a subjective audience is not needed. You can put whatever meaning you want on the symbols, but their behavior and functionality will not change, any more than a transistor will function differently if you give it another name.
Here’s an example of how complex the process is. Imagine I ask you to incrementally add random words to a list such that no two words use any of the same letters, and you must perform this exercise entirely in your head, so you can’t rely on a computer or even a pen and paper. If the first in the list was, say, “fox”, the second item excludes all words with the letters F, O and X. If the next word you choose is “tree”, then the third word in the list can’t have the letters F, O, X, T, R, or E in it.
As you can imagine, coming up with even a third word might start to get just a bit tricky, especially since you can’t easily visualize the excluded letters by writing down the words. By the time you get to the fourth, fifth and sixth words, the problem has spiraled out of control. Now imagine trying to add the billionth word to the list (imagine also that we’re working with an infinite alphabet so you don’t run out of letters) and you can imagine how difficult it is for even a computer to keep up. Needless to say, writing this kind of thing “by hand” is orders of magnitude beyond the capabilities of the brain.
My background lent itself well to this kind of work though. I’d spent years writing code and designing both analog and digital circuits, a process that at least visually resembled these diagrams in some way. I also had a personal affinity for combinatorics, which served me well as I helped with the design of software running on supercomputers that could juggle the often trillions of rules necessary to create a valid diagram of any reasonable complexity. This overlapped quite a bit with compiler theory as well, a subject I always found fascinating, and in particular compiler optimization, a field that wasn’t half of what it is today back then. A running joke among the linguistics team was that Big-O notation couldn’t adequately describe the scale of the task, so we’d substitute other words for “big”. By the time I left I remember the consensus was “Astronomical-O” finally did it justice.
Like I said, I could go on for hours about this subject, and would love to write at least an introductory book on the subject if it wasn’t still completely classified, but that’s not the point of this letter so I’ll try to get back on track.
The last thing I’d like to discuss is how I got copies of this material, what else I have in my possession, and what I plan to do with it in the future.
My Collection
I worked at PACL from 1984 to 1987, by which time I was utterly burned out. The sheer volume of details to keep in mind while working with the diagrams was enough to challenge anyone’s sanity, and I was really at the end of my rope with the military’s attitude towards our “need to know”. Our ability to get work done was constantly hampered by their reluctance to provide us with the necessary information, and I was tired of bureaucracy getting in the way of research and development. I left somewhere in the middle of a 3-month bell curve in which about a quarter of the entire PACL staff left for similar reasons.
I was also starting to disagree with the direction the leadership wanted to take as far as the subject of extra-terrestrials went. I always felt that at least some form of disclosure would be beneficial, but as a lowly CARET engineer I wasn’t exactly in the position to call shots. The truth is, our management didn’t even want us discussing non-technical aspects of this subject (such as ethical or philosophical issues), even among ourselves, as they felt it was enough of a breach of security to let civilians like us anywhere near this kind of thing in the first place.
So, about 3 months before I resigned (which was about 8 months before I was really out, since you don’t just walk out of a job like that with a 2 week notice), I decided to start taking advantage of my position. As I mentioned earlier, my DoD experience got me into an internal management role sooner than some of my colleagues, and after about a year of that kind of status, the outgoing searches each night became slightly less rigorous. Normally, we were to empty out any containers, bags or briefcases, then remove our shirt and shoes and submit to a kind of frisking. Work was never allowed to go home with you, no matter who you were. For me, though, the briefcase search was eventually enough.
Even before I actually decided to do it, I was sure that I would be able to sneak certain materials out with me. I wanted to do this because I knew the day would come when I would want to write something like this, and I knew I’d regret it until the day I died if I didn’t at least leave the possibility open to do so.
So I started photocopying documents and reports by the dozen. I’d then put the papers under my shirt around my lower back, tucked enough into my belt to ensure they wouldn’t fall out. I could do this in any one of a few short, windowless hallways on some of the lower floors, which were among the few places that didn’t have an armed guard watching my every move. I’d walk in one end with a stack of papers large enough that when I came out the other end with some of them in my shirt, there wouldn’t be a visible difference in what I was holding. You absolutely cannot be too careful if you’re going to pull a stunt like this. As long as I walked carefully they wouldn’t make a crinkling noise. In fact, the more papers I took, the less noise they made, since they weren’t as flimsy that way. I’d often take upwards of 10-20 pages at once. By the time I was done, I’d made out with hundreds of photocopies, as well as a few originals and a large collection of original photographs.
With this initial letter I have attached high resolution scans of the following:
A page from an inventory review with a photo that appears to depict one of the parts found in the Rajman sighting and parts very similar to the Big Basin craft.
The first 9 pages of one of our quarterly research reports.
Scans of the original photographs used in that report, since the photocopies obscure most of the details.
5 pages from a report on our ongoing analysis of the “language” (inappropriately titled “linguistic analysis”), depicting the kind of diagram just barely visible on the underside of the Big Basin craft.
This material is the most relevant and explanatory I could find on short notice. Now that these are up, IF I decide to release more in the future, I’ll be able to take my time and better search this rather large collection of mine that I’ve sadly never organized. I’m not sure what I’ll be doing with the rest of the collection in the future. I suppose I’ll wait and see how this all plays out, and then play it by ear. There are certainly risks involved in what I’m doing, and if I were to actually be identified and caught, there could be rather serious consequences. However, I’ve taken the proper steps to ensure a reasonable level of anonymity and am quite secure in the fact that the information I’ve so far provided is by no means unique among many of the CARET participants.
Besides, part of me has always suspected that the government relies on the occasional leak like this, and actually wants them to happen, because it contributes to a steady, slow-paced path towards revealing the truth of this matter.
Since Leaving CARET
Like I said, I left PACL in ’87, but have kept in touch with a great many of my friends and coworkers from those days. Most of us are retired by now, except of course for those of us that went on to get teaching jobs, but a few of us still hear things through the grapevine.
As for CARET itself, I’m not sure what’s become of it. Whether it’s still known by the same name, I’m quite sure it’s still active in some capacity, although who knows where. I heard from a number of people that PACL closed up shop a few years after I left, but I’ve still yet to get a clear answer on why exactly that happened. But I’m sure the kind of work we did there is still going strong. I’ve heard from a lot of friends that there are multiple sites like PACL in Sunnyvale and Mountain View, also disguised to look like unremarkable office space. But this is all second-hand information so you can make of it what you will.
Around 2002 or so I came across Coast to Coast AM and have been hooked ever since. I admit, I don’t take most of the show’s content as anything more than entertainment, but there have been occasions when I could be sure a guest was clearly speaking from experience or a well-informed source. For me, there’s just something very surreal about hearing all this speculation and so-called inside information about UFOs and the like, but being personally able to verify at least some of it as being true or false. It’s also a nightly reminder of how hectic things were in those days, which helps me enjoy my retirement all the more. Knowing I’m not part of that crazy world anymore really is something I enjoy on a daily basis, as much as I miss some of it.
Conclusion
What I’ve shared so far is only a very small portion of what I have, and what I know. Despite the very sheltered and insulated atmosphere within CARET, I did ultimately learn a great deal from various colleagues, and some of what I learned is truly incredible. I’d also like to say that for what it’s worth, during my time there I never heard anything about invasions, or abductions, or many of the more frightening topics that often pop up on Coast to Coast AM. That’s not to say that none of it is true, but in my time working alongside some of the most well-connected people in this field, it never came up. So at the very least I can say my intent is not to scare anyone. My view on the extra-terrestrial situation is very much a positive, albeit still highly secretive one.
One thing I can definitely say is that if they wanted us gone, we would have been gone a very, very long time ago, and we wouldn’t even have seen it coming. Throw out your ideas about a space war or anything silly like that. We’d be capable of fighting back against them about as much as ants could fight back against a stampede of buffalo. But that’s OK. We’re the primitive race, they’re the advanced races, and that’s just the way it is. The other advanced races let them live through their primitive years back in their day, and there’s no reason to think it will be any different for us. They aren’t in the market for a new planet, and even if they were, there are way too many planets out there for them to care about ours enough to take it by force.
To reiterate my take on the recent sightings, I’d guess that experimentation done in the last couple months on a device that, among other things, is capable of interfering with various crafts onboard invisibility has resulted in a sudden wave of sightings. It may not explain all of the recent events, but like I said, I’d bet my life that’s exactly what happened at Big Basin at least, and it’s probably related in some way to the Chad, Rajman and Tahoe sightings. So, despite all the recent fanfare over this, I’d say this doesn’t mean much. Most importantly, they aren’t suddenly “here”. They’ve been here for a long time, but just happened to turn unintentionally visible for brief periods recently.
Lastly, there are so many people selling books, and DVDs, and doing lectures, and all that, that I would like to reiterate the fact that I am not here to sell anything. The material I’m sharing is free to distribute provided it’s all kept intact and unmodified, and this letter is included. I tend to question the motives of anyone charging money for their information, and will assure you that I will never do such a thing. And in the future, just to cover all the bases, anyone claiming to be me who’s selling a DVD or book is most certainly not going to be me.
Any future releases from me will come from the email address I’ve used to contact Coast to Coast AM, and will be sent to them only. I’d like to make this clear as well to ensure that people can be sure that any future information comes from the same source, although I must be clear: at this time I do not have any future plans for additional information. Time will tell how long I will maintain this policy, but do not expect anything soon. I’d really like to let this information “settle” for a while and see how it goes. If I find out I’m getting an IRS audit tomorrow, then maybe this wasn’t too smart. Until then, I’m going to take it slow. I hope this information has been helpful.
FURTHER INFORMATION
Editor’s Note: The following important information was sent to me by a reader of this site. Her information rings true to me:
“The drone articles was reeeaally interesting!
Two thoughts on Isaac from a personal perspective. First, The power described in language: I’ve read many of his comments before, but in a book written about five thousand years ago. This caught my interest. This man struggles to describe concepts echoed in an ancient hebrew manuscript about the power in the hebrew language that God used to create the earth. (The Book of Creation, Sefer Yetzirah).
These are the quotes that I found most startling:
A language, that could quite literally execute itself, at least in the presence of a very specific type of field.
Geometric forms and patterns that fit together to form diagrams that are themselves functional.
Holographic because you can divide it up into the smallest chunks you want and still find a scaled-down but complete representation of the whole system.
Every element of each “diagram” is dependent on and related to every other element, which means no single detail can be created, removed or modified independently.
“Language” is entirely context-sensitive, which means that a given symbol could mean as little as a 1-bit flag in one context, or, quite literally, contain the entire human genome or a galaxy star map in another.
The ability for a single, small symbol to contain, not just represent, tremendous amounts of data.
Their technology, however, somehow merges the symbol and the meaning, so a subjective audience is not needed. You can put whatever meaning you want on the symbols, but their behavior and functionality will not change, any more than a transistor will function differently if you give it another name.
Anyone who has studied the mysterious side of Hebrew or Sanskrit would recognize this. I’ve also read accounts of the first ten commandments–that Moses broke–being described as holographic and fractal, yet in language terms that struggle to portray this long before these ideas existed commonly.
The letters rose up and rotated, and within each letter were reams of other information that could apparently be accessed. Like a compact computer. (The second set, however, was not. Just stone). So Isaac describes an anomalous language and yet he does not know he is describing something that has been precisely written about long before, as well as after, Noah’s flood. Pretty amazing. Watcher technology.
Second thought: regarding THAT technology. Isaac’s material reminds me of a quote from a second ancient manuscript. This is what God said to the fallen Watchers (advanced non human beings) who were charged with looking after mankind but blew it because of lust, selfishness, and rebellion.
1 Enoch, Chapter 16;2-3
-
2 And now as to the watchers who have sent thee to intercede for them, who had been aforetime in heaven,
vs.3 (say to them): “You have been in heaven, but all the mysteries had not yet been revealed to you, and you knew worthless ones, and these in the hardness of your hearts you have made known to the women, and through these mysteries women and men work much evil on earth.” 4 Say to them therefore: ” You have no peace.”‘
http://wesley.nnu.edu/biblical_studies/noncanon/ot/pseudo/enoch.htm
(End Quote)
Read more from Auricmedia:
[carousel-horizontal-posts-content-slider]